
With the continued threats from inside and outside their organizations, healthcare professionals have realized the need for robust identity governance and administration (IGA) policies.
Fortunately, electronic health record (EHR) vendors and third-party partners have developed software-based tools to automate IGA procedures for management of digital identities. These tools provide consistent business processes for reviewing, requesting, approving or revoking access, and managing passwords, underpinned by a common policy, role and risk model.
In our recently published whitepaper, Forward Advantage examines the history of IGA, its growing importance for healthcare organizations, and the steps needed to optimize an IGA infrastructure.
Background and benefits of IGA
The concept of identity governance and administration grew out of mandates set by the Health Insurance Portability and Accountability Act (HIPAA) of 1996 and the Sarbanes-Oxley Act of 2002 as a way to improve transparency and manageability of digital information.
By 2018, IGA had grown to a $3.04 billion market, driven by increased fraud and theft, new regulations governing protected health information (PHI), and the movement of healthcare providers and support staff.
And just as healthcare technology has evolved to offer new digital tools for providers and patients, IGA has empowered organizations to more efficiently assign and withdraw access to important systems, reducing IT staff workload and ensuring compliance with industry regulations.
As IGA grows in healthcare, long-term view is needed
The need for improved identity governance and administration in healthcare is reflected in the cybersecurity surveys published by organizations such as the College of Healthcare Information Management Executives (CHIME), the Association for Executives in Healthcare Information Security (AEHIS), and the Healthcare Information and Management Systems Society (HIMSS) that show the top concerns of healthcare executives.
In 2019, HIMSS reported that nearly half of respondents cited online scam artists and negligent insiders as the biggest threats facing their organizations, and they are increasingly looking to IGA to improve their security posture against these threats.
Healthcare IT executives often approach IGA as a short-term solution — an understandable reaction, given the urgency that they face to address ongoing security threats — but the best approach is actually to see IGA as a long-term solution, ensuring that it can be optimized over time while resolving immediate issues along the way.
What can healthcare organizations do?
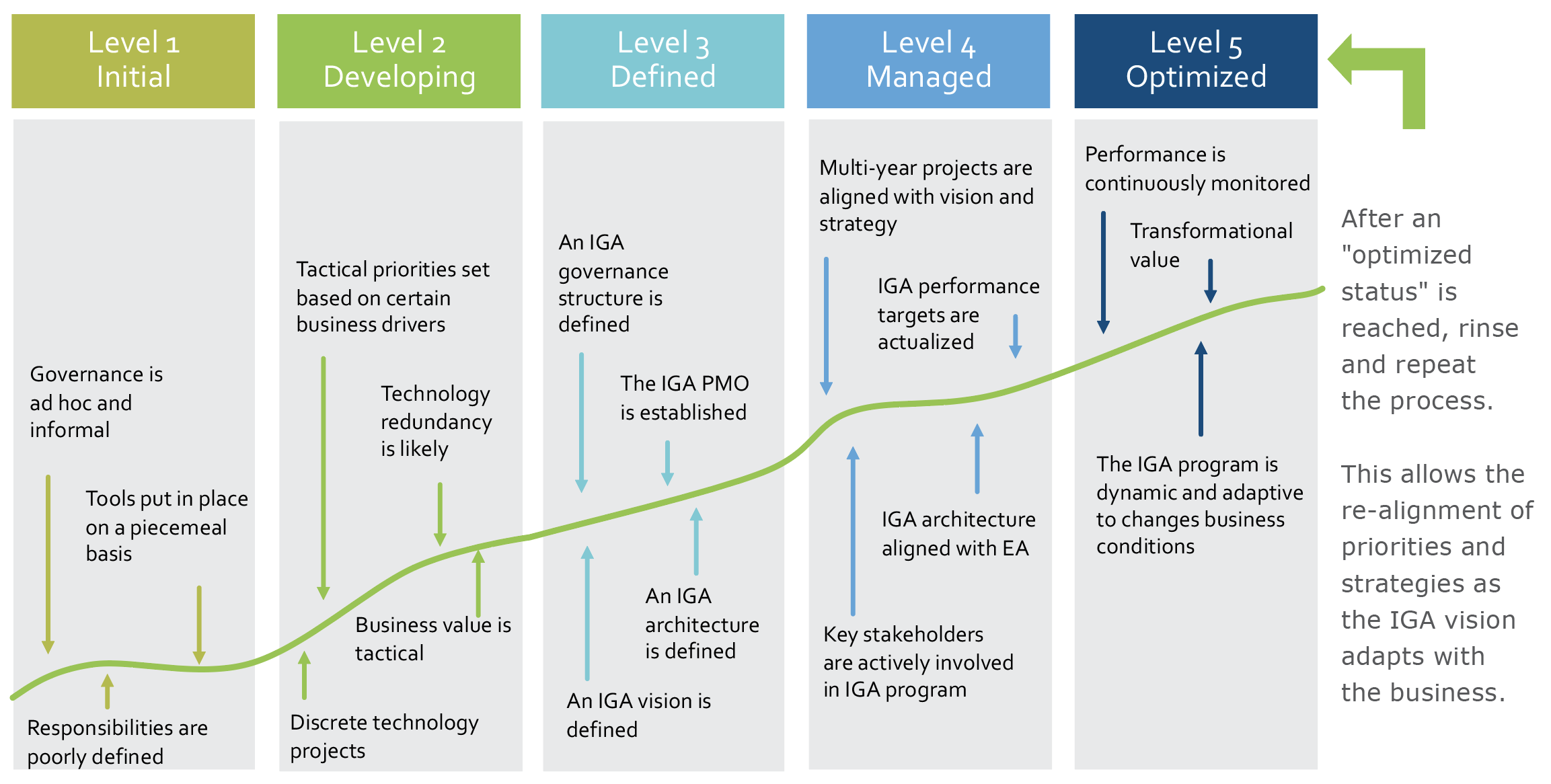
Forward Advantage has developed the following chart to illustrate what a healthcare organization’s journey toward IGA may look like.
It’s important to note that IGA is not a one-size-fits-all solution, nor is it a single project — it’s a strategy to ensure that an organization’s security posture is stronger than it was before the program began.
It’s never too early to start planning for an identity governance program.
To learn more about how to implement IGA at your organization, including how to assess your technical environment, prioritize the requirements for software solutions and services, and continue to optimize your system, please download the Forward Advantage whitepaper, Identity Governance & Administration in Healthcare.
Sign up today for MEDITECH's 2021 Physician and CIO Forum, Sept. 29 and 30.




